SECURITY ADVISORY: DarkSword iOS Exploit and its Impact on Blockchain Payload Integrity
The recent disclosures surrounding the DarkSword iOS malware have sent shockwaves through the mobile security landscape. As someone who spends my days auditing smart contracts and building secure blockchain infrastructure at Ubitquity, I want to cut through the noise and clarify exactly how an OS-level exploit like this threatens digital assets.
We frequently remind the community that the blockchain is immutable and cryptographically secure. That fact has not changed. DarkSword does not hack Ethereum, Bitcoin, or any other distributed ledger. The vulnerability lies entirely at the endpoint: your mobile device.
When the operating system used to construct and sign a blockchain payload is compromised at the kernel level, the integrity of the transaction is shattered before it ever reaches the mempool. Here is a technical breakdown of how an exploit of this caliber theoretically manipulates blockchain payloads, complete with visual mappings of the exact moment transaction integrity fails.
1. OS Level Payload Spoofing (Clipboard Hijack)
When you initiate a transaction in a mobile wallet, the application constructs a payload containing the recipient address, value, and transaction data. Because DarkSword utilizes kernel bypass vulnerabilities, it gains root-equivalent access to device memory and clipboard functions.
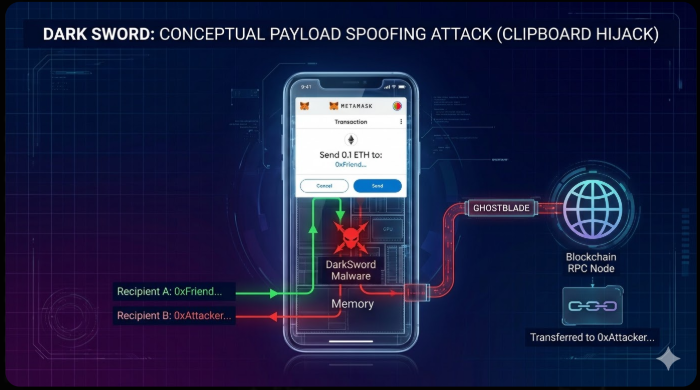
Diagram Breakdown:
The user intends to send funds to a known contact. DarkSword has achieved root-level access via the kernel exploit and is actively monitoring the device clipboard and memory.
- Intercept: Right as the user copies the address or confirms the send command, the malware intercepts the function call.
- Swap: It dynamically replaces the destination address with the attacker-controlled address.
- Broadcast: The wallet application, completely unaware it is using manipulated inputs, signs the transaction. The resulting payload is broadcasted to the blockchain RPC node.
- Result: The transaction is immutable and confirmed on the blockchain, but the funds are transferred to the attacker. The endpoint failure completely compromises the transaction integrity.
2. Private Key Exfiltration and Off Site Forgery
The most severe threat vector does not involve altering a payload on the victim device. It involves stealing the ability to generate valid payloads entirely. This highlights the rapid data extraction capabilities of DarkSword.
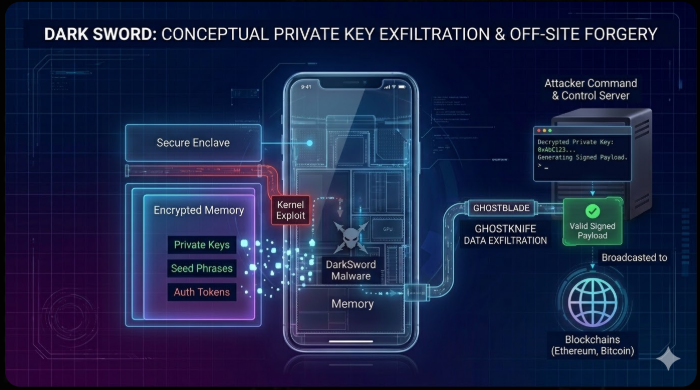
Diagram Breakdown:
This diagram is a breakdown of digital identity theft at the application layer.
- Exploit and Scrape: The DarkSword malware uses its kernel exploit to gain deep access to device memory. It actively hunts for application-specific data, scraping memory for stored unencrypted private keys, wallet seed phrases, and active authentication tokens.
- Exfiltrate: This data is bundled and sent via the GHOSTBLADE pipeline back to an attacker command and control server. The infection on the phone typically deletes itself at this stage to avoid forensic detection.
- Forge: The attacker now possesses the victim's cryptographic keys. They use this data to construct entirely new, malicious transaction payloads off-site.
- Broadcast: The attacker system broadcasts the valid, signed payload to the network, draining the assets. The victim's phone was simply the tool for the initial theft of identity.
3. Malicious Calldata Injection and Blind Signing
For users interacting with Web3 decentralized applications, the risk profile is significantly higher. Smart contract interactions require complex payloads containing specific calldata. DarkSword can hijack a mobile dApp browser session and invisibly replace the intended calldata.
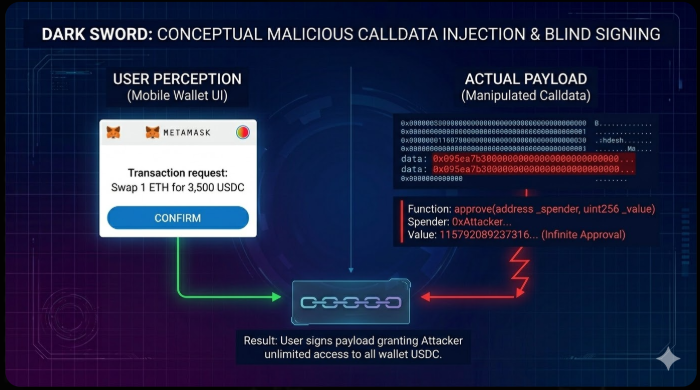
Diagram Breakdown:
This diagram demonstrates the disconnect between user perception and technical reality when a device is compromised.
- Perception: The user is on a mobile phone interacting with a wallet prompt. They see a request to execute a standard token swap transaction and proceed based on this visual data.
- Reality: In the background, DarkSword has used its root access to inject malicious calldata into the wallet session. The raw data is now an instruction to approve a specific attacker-controlled smart contract to manage the wallet funds, setting the value field to a massive hexadecimal number.
- Result: When the user confirms the prompt via blind signing, they are not executing a swap. They are cryptographically signing a payload that grants an attacker smart contract infinite permission to withdraw all designated assets from the wallet.
Securing the Endpoint
What these visualizations show is that the blockchain's core architecture remains solid. The cryptography works. The immutable ledger works.
The entire system fails when the endpoint is controlled by the attacker. If the OS can manipulate clipboard data, memory storage, or dApp sessions, then the mobile phone is essentially a backdoor directly into your wallet. In this environment, your private key is just another variable for the malware to control.
The old axiom needs an update: if you do not control the integrity of your endpoint, you do not control your keys.
Relying on a daily driver mobile phone as a primary hot wallet is a critical security oversight when facing advanced malware. I strongly advise the community to migrate significant holdings to dedicated hardware wallets (cold storage) and immediately patch any vulnerable iOS devices to version 18.7.6 or 26.3.1.
Stay vigilant, audit your approvals, and always verify your payloads.