NETTWERKED White Hat Division:
Tactical Threat Intel Briefing
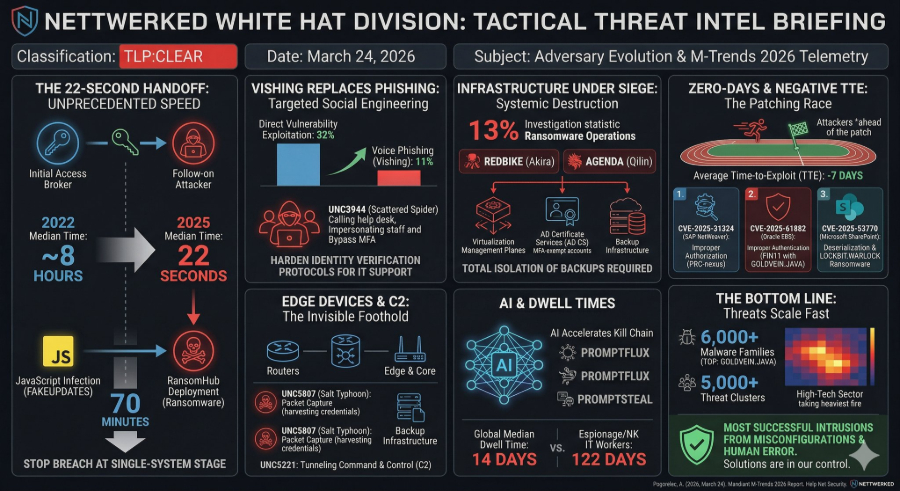
Listen up. The adversary landscape is shifting fast, and the window for defensive intervention is practically gone. Based on telemetry from over 500,000 hours of 2025 incident response data, threat actors are streamlining operations, bypassing traditional detection, and moving with unprecedented speed.1 Here is the unvarnished reality of what we are facing on the wire right now.
The 22-Second Handoff
The division of labor between Initial Access Brokers and follow-on attackers has hit breakneck speeds. In 2022, we had about eight hours to detect an initial breach before access was handed off. In 2025, that median time collapsed to just 22 seconds. Attackers are bypassing underground forum sales entirely and dropping secondary malware directly. In one documented case, it took only 70 minutes from a FAKEUPDATES JavaScript infection to the deployment of RansomHub across Windows and virtual servers. If your SOC is only hunting for late-stage ransomware behavior, you are already too late. Stopping the breach at the single-system stage is our only viable move.
Vishing is Replacing Phishing
Volume-based email phishing is dying out, replaced by highly targeted, interactive social engineering. Voice phishing has surged to the second-most common initial infection vector at 11%, trailing only direct vulnerability exploitation at 32%. Threat clusters like UNC3944 (Scattered Spider) are directly calling help desks, impersonating staff, and talking their way through MFA and password resets. Automated technical controls cannot patch human empathy. We need to harden our identity verification protocols for IT support immediately.
Infrastructure Under Siege
Threat actors aren't just stealing and encrypting data anymore. They are systematically destroying our ability to recover. Ransomware operations made up 13% of investigations, with REDBIKE (Akira) and AGENDA (Qilin) leading the pack. Operators are actively targeting virtualization management planes, identity services, and backup infrastructure. They are exploiting misconfigured Active Directory Certificate Services (AD CS) to create MFA-exempt admin accounts and extracting privileged credentials to lock defenders out during a crisis.
Attackers are also compressing Virtual Hard Disks directly on the hypervisor to bypass guest OS data loss prevention controls, then encrypting the datastore files outright. Total isolation of our backup infrastructure is no longer optional.
Zero-Days and Negative TTE
The patching race has fundamentally changed. The average Time-to-Exploit (TTE) has turned negative and is currently estimated at -7 days. This means threat clusters are actively exploiting vulnerabilities before vendors even release a patch. Three major zero-days drove widespread exploitation last year:
- CVE-2025-31324 (SAP NetWeaver): Improper authorization allowing unauthenticated file uploads, heavily exploited by PRC-nexus espionage groups.
- CVE-2025-61882 (Oracle EBS): Improper authentication leading to unauthenticated RCE, leveraged by FIN11 using the GOLDVEIN.JAVA downloader.
- CVE-2025-53770 (Microsoft SharePoint): Deserialization vulnerability chained into "ToolShell" to drop LOCKBIT.WARLOCK ransomware.
The Vulnerability of Edge Devices
Sustained campaigns are now heavily targeting proprietary edge and core network devices. Because these devices usually cannot run standard EDR tools, actors are using them to establish invisible footholds. For example, UNC5807 (Salt Typhoon) used native packet capture on edge devices to harvest cleartext credentials, while UNC5221 tunneled command and control traffic right through legitimate third-party services to bypass network filtering.
AI and Dwell Times
AI isn't the primary root cause of the breaches we are seeing, but it is accelerating the kill chain. Malware families like PROMPTFLUX and PROMPTSTEAL are actively querying LLMs during execution to evade detection, while tools like QUIETVAULT hunt for developer tokens.
Meanwhile, the global median dwell time crept up to 14 days in 2025. Deeply embedded espionage and insider threats like North Korean IT workers using false identities are lurking undetected for a massive median of 122 days.
The Bottom Line
The threats are scaling fast. There are over 6,000 malware families (with GOLDVEIN.JAVA taking the top spot) and 5,000 threat clusters currently active, with the High-Tech sector taking the heaviest fire. The good news is that most successful intrusions still stem from systemic misconfigurations and human error, which means we control the solutions.
References
- Pogorelec, A. (2026, March 24). Attackers are handing off access in 22 seconds, Mandiant finds. Help Net Security. https://www.helpnetsecurity.com/2026/03/24/mandiant-m-trends-2026-report/